NEXUS-AI Platform
Your enterprise has 45 non-human identities for every employee — and nobody is governing them. NEXUS-AI finds every service account, API key, and certificate your tools miss, assigns an owner, and enforces policy 24/7. Before your next breach does it for you.

From Identity Chaos to Governance
NEXUS-AI brings order to your non-human identity sprawl
Right Now, Inside Your Enterprise
45:1
NHIs Per Employee in Your Org
68%
Are Stale — Never Rotated
82%
Have Zero Accountability
$4.88M
Avg. Breach Cost (IBM 2024)
The Next Breach Won't Come Through a Human Account
Non-human identities outnumber your employees 45-to-1. They authenticate to your most critical systems, hold powerful privileges, and operate without MFA, without session limits, and without anyone watching. When attackers compromise a service account — and they will — there's no login alert, no password reset prompt, no user to call.
Your IGA platform wasn't built for this. Neither was your PAM vault. They assume human users who type passwords and respond to MFA prompts. NHIs are created programmatically, authenticate with embedded credentials, and accumulate privileges that nobody reviews — because nobody knows they exist.
That's the gap NEXUS-AI closes. Compound AI — multiple specialized models working in concert — continuously discovers, classifies, assigns ownership, and governs every non-human identity in your estate. Not quarterly. Not when the auditor asks. Every hour of every day.

Compound AI Governance Engine
Multiple specialized AI models collaborate to discover, classify, attribute, and govern — each model contributing what it does best.
Data Sources
Discover
Static analysis + runtime observation + infrastructure metadata. Finds NHIs that single-technique scans miss.
Classify
Type, privilege level, blast radius, rotation status. Risk scores drive governance priority.
Attribute
Code repo analysis + deployment metadata + dependency graphs. Every NHI gets a human owner.
Govern
Rotation enforcement, anomaly detection, policy compliance, audit evidence. 24/7 continuous.
Continuous Outputs
Six Problems You Stop Losing Sleep Over
Find Every NHI — Even the Ones You Don't Know Exist
Your last audit missed them. NEXUS-AI won't. Compound AI combines static analysis, runtime observation, and infrastructure metadata to surface embedded credentials, orphaned service accounts, shadow API keys, and forgotten certificates — across every cloud, every repo, every pipeline.
Know Which NHIs Can Bring Down Your Business
Not all NHIs are equal. NEXUS-AI risk-scores every identity by privilege level, blast radius, rotation status, and behavioral patterns — so your team remediates the ones that could cause a $4.88M breach first, not the ones that sort alphabetically.
End the "Who Owns This?" Problem Forever
Every security incident involving an NHI starts with the same question: "Who owns this service account?" NEXUS-AI traces ownership through code repos, deployment pipelines, and dependency graphs — attributing every NHI to a responsible human. No spreadsheets. No guessing.
Rotate Credentials Before Attackers Exploit Them
That API key hasn't been rotated in 18 months. The service account password is from 2019. NEXUS-AI enforces rotation policies automatically for supported platforms and escalates the rest — with real-time compliance dashboards that make audit day boring.
Catch Compromised NHIs Before the Damage Spreads
A service account authenticating from a new IP at 3 AM with elevated privileges? NEXUS-AI knows that's wrong because it has learned what "normal" looks like for every NHI in your estate. Alert on deviations in seconds — not during the next quarterly review.
Walk Into Every Audit With Evidence Already Generated
HIPAA, SOX, PCI-DSS, NIST 800-53, SOC 2 — NEXUS-AI generates compliance evidence continuously, not the week before your auditor arrives. Your NHI posture is always audit-ready. Your compliance team will send you a thank-you note.
From discovery to governance in weeks — not quarters.
How It Works
Connect — 30 Minutes to First Scan
Point NEXUS-AI at your cloud providers, identity platforms, code repositories, and CI/CD pipelines. Pre-built connectors for AWS, Azure, GCP, Okta, SailPoint, CyberArk, GitHub, GitLab, and Kubernetes. No agents to install.
Discover — See Your Real Attack Surface
Within hours, NEXUS-AI surfaces the NHIs your existing tools can't see — embedded credentials in code, orphaned service accounts from departed engineers, shadow API keys created outside governance, certificates expiring next week.
Classify & Attribute — Risk-Ranked With Owners Assigned
Every NHI gets a risk score, a blast radius assessment, and a human owner. Your CISO sees a prioritized dashboard. Your security team knows exactly what to fix first and who to call.
Govern — Continuous, Not Quarterly
From day one, NEXUS-AI runs 24/7 — rotating credentials, detecting anomalies, discovering new NHIs as they're created, and generating audit evidence automatically. Your NHI governance posture improves every single day.
Your Existing Tools Were Never Designed for This
You've invested millions in IGA and PAM. Here's why they still can't solve the NHI problem.
IGA Platforms: Built for Humans
Your IGA uses static rules and connectors designed for human joiners, movers, and leavers. NHIs don't follow that lifecycle. They're created in code, embedded in configs, and proliferate across environments your IGA connector never touches. NEXUS-AI uses compound AI to find what rules-based discovery structurally cannot.
PAM Vaults: Guard the Key, Ignore the Door
PAM vaults credentials but can't tell you who created the service account, what it accesses, or whether it's still needed. During an incident, you're digging through Confluence pages from 2021. NEXUS-AI resolves ownership in seconds through code and deployment graph analysis.
Quarterly Reviews: 90 Days Too Late
An NHI created on Monday can be compromised by Tuesday and exfiltrate data for 88 days before your next quarterly review. NEXUS-AI discovers new NHIs in real time, detects anomalies in seconds, and generates compliance evidence continuously. The gap between "created" and "governed" shrinks to zero.
Every Non-Human Identity Type
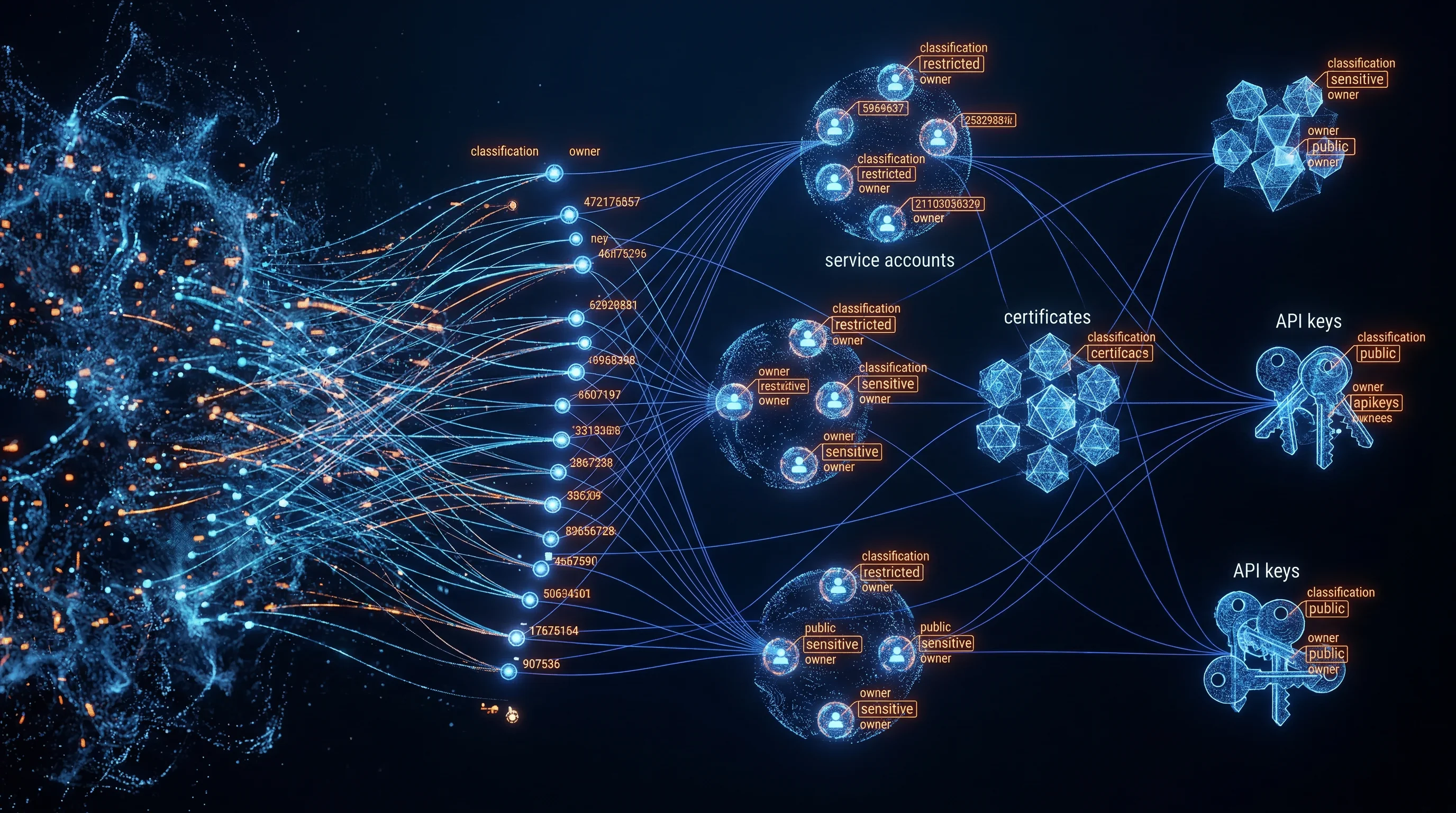
Service Accounts
AD, cloud IAM, database
API Keys
REST, GraphQL, webhook
Certificates
TLS, mTLS, code signing
OAuth Tokens
Client credentials, refresh
Cloud Workloads
IAM roles, managed identity
CI/CD Secrets
Pipeline tokens, deploy keys
Embedded Credentials
Config files, env vars
Bot Accounts
RPA, automation, integrations
Supported Environments
NEXUS-AI is a proprietary product of TechSquad Consultants LLC. Patent pending. The compound AI architecture, discovery algorithms, and ownership attribution engine are trade secrets of TechSquad Consultants LLC. Vendor-agnostic by design — NEXUS-AI integrates with your existing identity stack, not against it.
How Many Ungoverned NHIs Are in Your Environment Right Now?
Most enterprises discover 3-5x more NHIs than they expected in the first scan. Book a 30-minute demo — we'll show you what your existing tools are missing.
No sales pitch. Just a live scan walkthrough with a principal architect.
Book Your Demo